One Platform.
Every Assessment Type.
Used by internal security teams, consultancies, and red teams to standardize delivery across every assessment type.
Your Methodology, Your Platform
Neuron adapts to your methodology, not the other way around. Every assessment type gets the same powerful toolset.
Flexible Templates
Custom finding templates per assessment type. Web app, API, cloud—each gets purpose-built structures.
Unified Library
Build findings across ALL assessment types. Web OWASP findings live alongside AD misconfigurations.
Same Speed
AI content generation works for web, mobile, cloud, and beyond. 3x faster reporting on every engagement.
Complete Portfolio
Manage all assessment types from a single dashboard. Consistent QA across your entire practice.
Built for How You Actually Work
From web applications to adversary simulation, Neuron provides purpose-built workflows for every engagement type.
Web Application
OWASP-aligned templates for XSS, SQLi, and business logic flaws. Full evidence management accelerates your web app testing workflow.
API Security
Document broken authentication, data exposure, and authorization flaws. Track endpoints and attack chains systematically.
Cloud Security
AWS, Azure, GCP findings structured for IAM misconfigurations, storage exposures, and infrastructure-as-code issues.
Active Directory
Capture Kerberoasting, DCSync, and privilege escalation paths. Credential vault tracks hashes and attack chains through the domain.
See it in actionMobile Application
iOS and Android assessments with platform-specific templates. Track certificate pinning, local storage, and API communication issues.
Network / Internal
Import from Nmap, Nessus, Nexpose. Host and service tracking with automatic dangerous service detection and vulnerability enrichment.
Red Teaming
Document full adversary simulation campaigns. Track objectives, attack paths, and credential chains across complex multi-phase operations.
Social Engineering
Phishing campaigns, vishing, and physical access findings documented with the same rigor as technical vulnerabilities.
Purpose-Built for Every Scope
Web Application Security at Scale
From OWASP Top 10 to complex business logic flaws, Neuron streamlines your web application testing workflow. Track authentication bypasses, injection vulnerabilities, and session management issues with structured evidence collection that makes report writing effortless.
- OWASP-aligned finding templates ready to customize
- Screenshot and request/response evidence management
- Retest tracking for remediation verification

API Security Made Systematic
Modern applications are API-first, and so is Neuron. Document broken authentication, authorization flaws, and data exposure issues with the same rigor as traditional web assessments. Track complex attack chains across multiple endpoints.
- Track endpoints, methods, and authentication schemes
- Evidence collection for multi-step API attack chains
- Clear remediation guidance for development teams

Cloud Security Across Providers
AWS, Azure, GCP—cloud misconfigurations don't fit traditional vulnerability templates. Neuron's flexible finding structure captures IAM issues, storage exposures, and infrastructure-as-code problems with full context that cloud teams can act on.
- Findings structured for cloud-native issues
- Track resources across accounts and subscriptions
- Executive summaries that explain cloud risk to stakeholders

Active Directory Attack Paths, Documented
Kerberoasting, DCSync, forest trusts—AD assessments produce complex findings that don't fit checkbox scanners. Neuron captures full attack paths with credential chains and privilege escalation routes that demonstrate real business impact.
- Credential vault tracks captured hashes and tokens
- Document lateral movement and trust relationships
- AI generates executive-friendly AD risk explanations

iOS and Android Testing
iOS and Android applications present unique challenges—certificate pinning, local storage, biometric bypasses. Neuron provides platform-specific templates that capture mobile-native vulnerabilities with the evidence developers need to fix them.
- Platform-specific templates for iOS and Android
- Track API communication and authentication issues
- Evidence management for dynamic and static analysis

Network and Infrastructure
Import results from your favorite scanners and let Neuron handle the rest. Automatic dangerous service detection, vulnerability enrichment from NVD and CISA KEV, and structured findings that turn raw scan data into actionable reports.
- Import from Nmap, Nessus, Nexpose, and more
- Automatic CVE enrichment and exploit availability
- Dangerous service flagging for quick wins

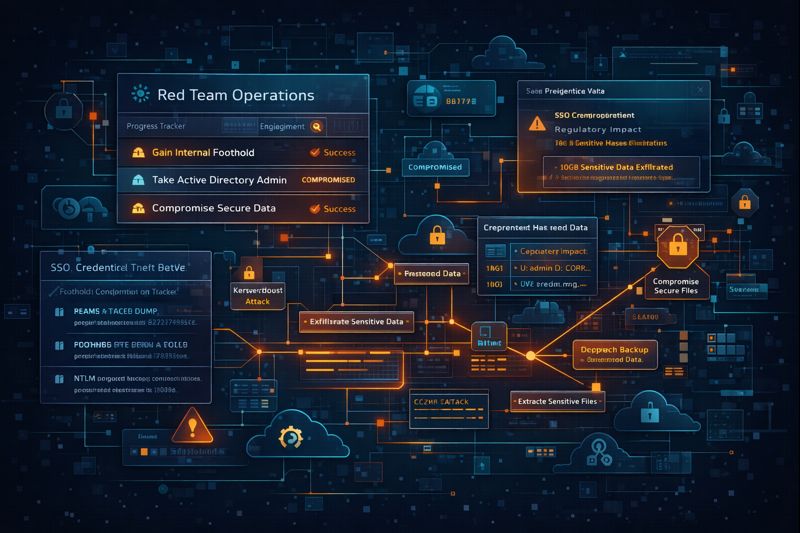
Red Team Operations
Adversary simulations span weeks and involve complex attack chains. Neuron tracks objectives, documents lateral movement, and maintains credential chains across multi-phase operations—giving stakeholders the full picture of organizational risk.
- Track campaign objectives and success criteria
- Document attack paths across multiple phases
- Credential vault for captured access throughout the operation
Social Engineering
Phishing campaigns, vishing calls, and physical access attempts deserve the same documentation standards as technical findings. Neuron captures human-factor vulnerabilities with structured evidence and clear remediation paths.
- Template-based findings for phishing and vishing
- Track campaign metrics and success rates
- Actionable awareness training recommendations

Ready to Transform Your Security Practice?
See how Neuron helps security teams replace fragmented tools with a single platform for offensive security—bringing structure, visibility, and consistency to every engagement.
Platform